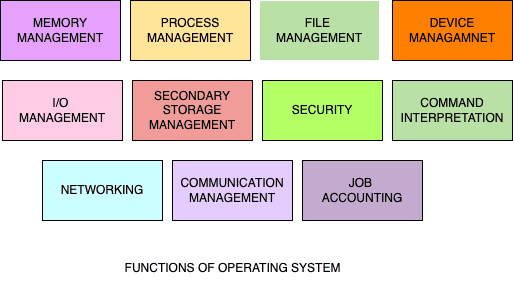
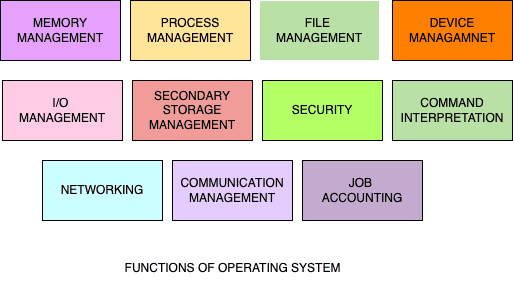
What is an Operating System?A An example of software that creates the environment for other software or applications to operate on the system is the operating system. In order for the computer to run, it performs or operates on the backend. Every electronic device you use, such as a computer, smartphone, or other comparable gadget, has a unique OS.The OS of the device you are using is what gives it its Various operating system kinds exist depending on the devices and user preferences. and a maker of devices. The OS is something you should know a lot more about if you work in or want to work in the information technology industry. Origins of OS In order to manage tape storage, operating systems were originally created in the late 1950s.The first OS was built by the General Motors Research Lab for their IBM 701 in the early 1950s.Operating systems first began utilising discs in the middle of the 1960s.The initial Unix OS version was created in the late 1960s.Microsoft’s original operating system was DOS. It was created in 1981 using 86-DOS software that was purchased from a Seattle-based company.When a GUI was developed and combined with MS-DOS in 1985, the modern, widely used OS Windows was born. Also read: How does culture impact ESA? Functions of operating system The following are the typical functions of an operating system: Memory management: itis the process of controlling both primary and secondary memory. An entire programme must be present in memory in order for it to be executed. For the duration of the job, it moves the processes to the primary memory and then moves them back. It coordinates the usage of multiple memory types and allocates the necessary amount of memory to the processes using several techniques, including best, worst, and first fits. Memory management keeps track of all memory usages, including which areas are occupied by which processes and which areas are unoccupied. It also deallocates memory when a process no longer needs it. Process Management: A programme is merely a collection of executable code; it is a passive entity. The CPU executes jobs or programmes, which are referred to as processes. The process management system handles all operations connected to processes, including process communication, multitasking, synchronisation, creation, deletion, job scheduling, suspension, and resumption, as well as addressing deadlocks and many other tasks. Device management: Device management is also referred to as an I/O controller. It detects the devices and sets up the necessary drivers so that they can function. The user may need to manually instal the drivers for some devices. Device management is in charge of tracking tasks, specifying which processes receive devices when and for how long. The device is efficiently allocated, and when it is no longer needed for that process, it is also de-allocated. File management: It controls all operations involving files, including naming, storing, organising, retrieving, sharing, and protecting them. Secondary Storage Management: Systems include multiple levels of storage, including primary storage, secondary storage, and cache storage. In order for a programme that is now running to reference it, instructions and data must be kept in primary storage or cache. Security: A system can support numerous concurrent users, and if multiple processes are permitted to run simultaneously, the OS is required to safeguard these processes from one another’s actions. Additionally, it permits various people access to the memory, processes, files, and devices. Networking: A technique called networking makes it possible to link many devices at once and share resources among them. It is a distributed processor in which the memory, processor, clock, or hardware are not shared and communication takes place over a network instead. Command interpreter: A command interpreter is a programme that acts as a conduit between the user and the operating system and interprets commands entered by the user via scripts or input devices. It receives the user’s command, decodes it, and aids in activating the necessary system resources to complete the task. Job accounting: The function of job accounting is to keep track of time and resources used by different jobs and users. Communication Management: Coordination and allocation of compilers, interpreters, and other software resources among the many computer system users. Examples of computer operating system The most widely used and popular operating system on computers today is Microsoft Windows, with Windows 11 being the newest version. Computers that are compatible with IBM and PC utilise the operating system. Apple macOS macOS is a Unix operating system introduced and marketed by Apple Inc. since 2001. macOS is the primary operating system used by apple desktop and MacBooks. Chrome OS and Chromium An operating system for Google Chrome books is called Chrome OS. Linux Linux is an operating system that runs on PCs and IBM-compatible systems for free and open source. Since the operating system is free and open source, several different versions of Linux, such as Ubuntu, Debian, Red Hat, and Slackware, have been developed. Examples of mobiles operating systems Here are some examples of operating system used by mobile devices such as smart phones and tablets. Android : It is an operating system for tablets and smartphones. Due to how many smartphones utilise a version of the Android operating system, Android is currently the most widely used OS worldwide. iOS by Apple The operating system that is utilised with the Apple iPhone and iPads is called Apple iOS. Additional mobile operating systems The BlackBerry OS, Embedded Linux, Palm OS, Symbian OS, Windows Embedded, and Windows Phone are other embedded and mobile OS. OPERATING SYSTEM BENEFITS: It guarantees effective use of the hardware. It enables numerous programmes or processes to execute simultaneously. The same equipment and procedure can be used by several users simultaneously. The graphical user interface that the OS offers makes managing, configuring, and using the hardware simple. It conceals from users the hardware’s finer points. It oversees and regulates how the processes are carried out. Use of open source OS is free. DISADVANTAGES OF OPERATING SYSTEM: You risk losing any data you have stored in your system if an issue arises and the OS crashes. A pricey and well-known operating system like Windows also requires yearly licence renewal. Threats could arise at any time, thus it is not completely secure. It might be open to assault. Use of open source operating systems is difficult.

Nice blog